Web Access Management, Federated SSO & Externalized Authorization Management
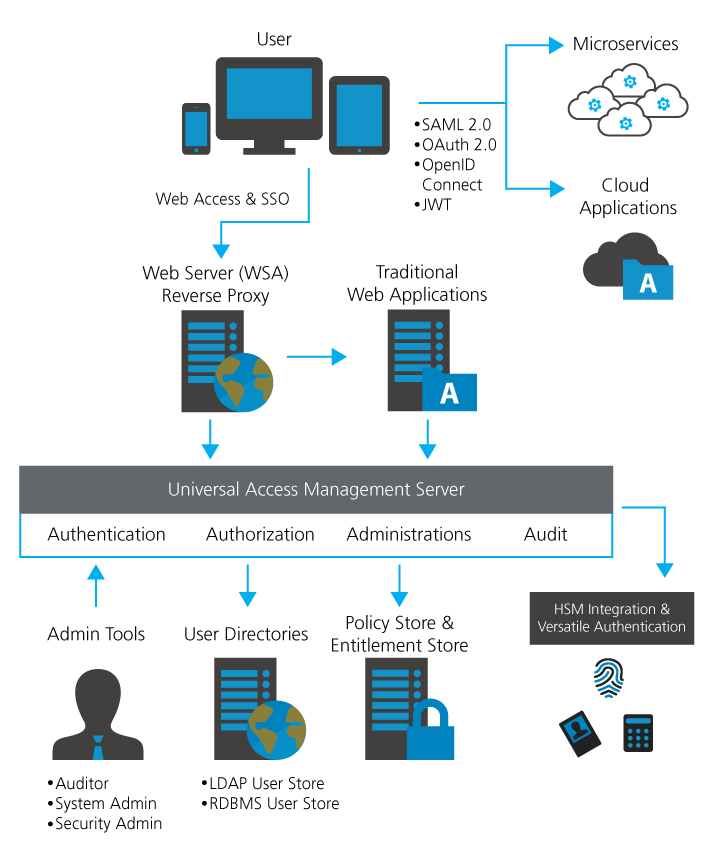
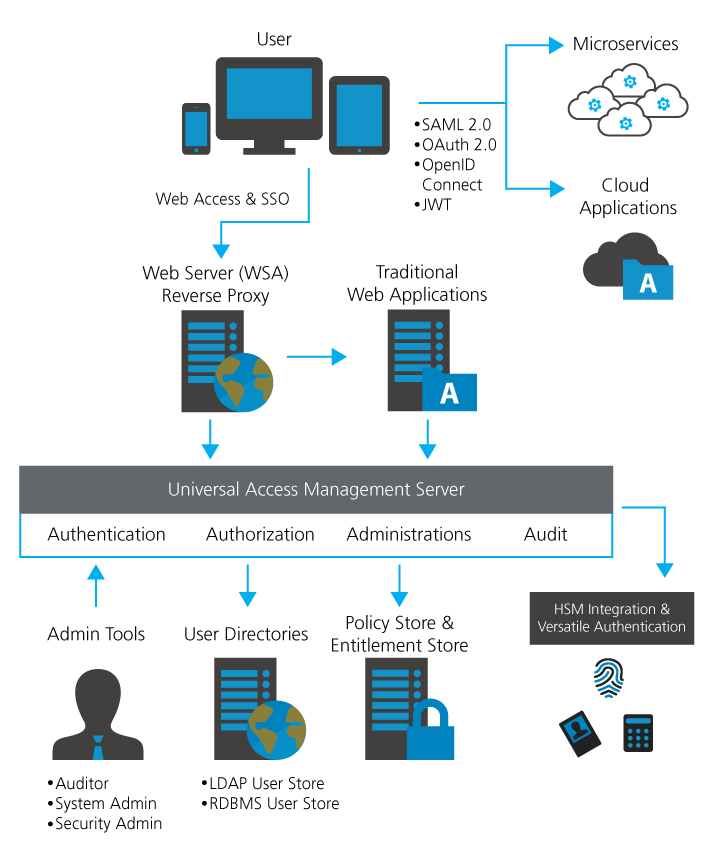
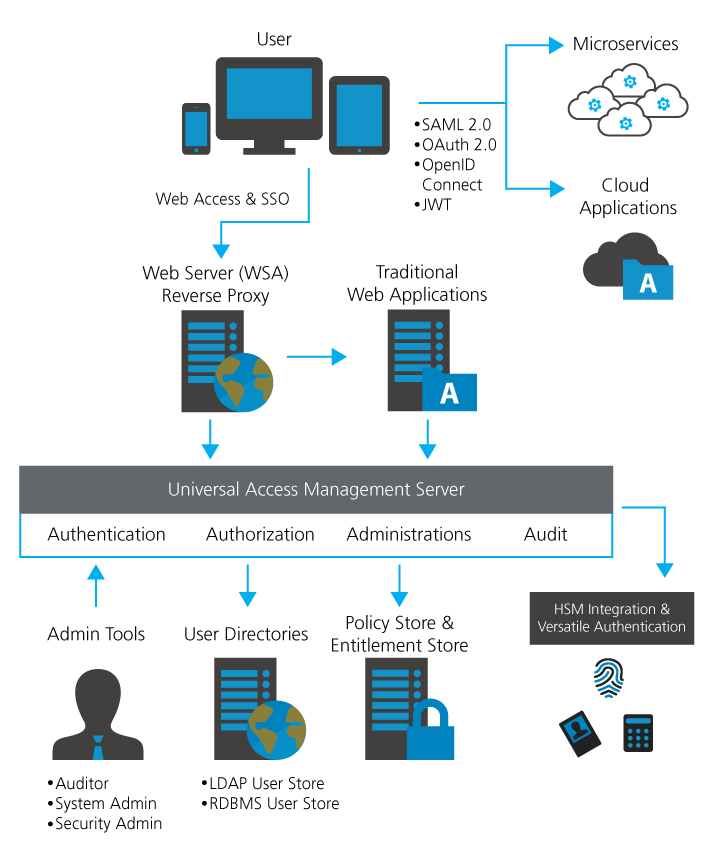
AccessMatrix™ Universal Access Management (UAM) is a comprehensive web single sign-on (SSO), web access management, federated single sign-on (SSO), and social network login, externalized authorization management, and hierarchy-based delegated administration system. Leveraging the AccessMatrix™ technology, UAM fulfills the most rigorous form of application security by providing secure Administration, Authentication, Authorization, and Audit services (4As) to business applications within your organization.
Built on the regulatory requirements and standards in banking & finance sector, UAM enables custom enterprise/ internet applications to access a common set of IAM (Identity & Access Management) services and lowers the integration cost.
Improving Application Security
UAM provides a set of security APIs for developers to tightly integrate web and non-web applications. With UAM’s Web Security Agents (WSA) and Application Security Agents (ASA), access to the resources within web servers and application servers are protected based on the access control policy defined by the security administrators.
This policy-driven approach greatly simplifies user administration and application integration. UAM is built on the AccessMatrix framework and UAM inherits the salient features of AccessMatrix, in addition to its own features.
Providing Flexible Agent Technology And Policy-Driven Access Control
The UAM security infrastructure is designed to secure multi-tier applications, either web-based or non web – based, running on multiple heterogeneous platforms. The AccessMatrix hierarchical model allows organizations to deploy a single security infrastructure for easy integration with multiple applications. All access control decisions are made by the AccessMatrix security server.
The UAM solution is highly scalable, promotes software re-use and reduces application maintenance and support efforts.
Key Features :
- Embedded Strong Authentication, Web SSO, Federated SSO and Enterprise SSO on the same back-end
- Extensible Pluggable Authentication Modules support strong authentication requirements using SMS, hardware and software tokens
- Flexible and open APIs are provided for ease of integration and code re-use for security 4As services
- Support SAML, OAuth and OpenID Connect
- Tamper-evident Audit Trail
- Scalable
Key Benefits :
- Ease up integration and deployment efforts with native integration with existing LDAP, AD and JDBC directories, i.e. no schema changes or no information written to the external user stores
- Provide a highly scalable, open and reliable platform to support demanding operational requirements such as automatic failover, horizontal & vertical scaling and 24×7 operations
- Provide security management and enforcement of 4As, including authentication policies, authentication methods, user stores and administration delegation, as well as audit compliance reporting
- Lower integration and operational costs with a common set of IAM services for custom enterprise and internet applications to access

