Rise of Mobile Security
In the beginning, companies use desktops as a means for its employee to access the company network and data in order to protect the security of their intellectual property (IP). However, with the rise of remote work, following the Covid-19 pandemic, there has been an increasing emphasis on mobility and mobile devices which have become the frontier for workplace mobility.
As the usage of our mobile devices shift from personal to business use, this poses a significant threat to corporate security due to its high touch points. Internet browsing is no longer limited to desktops but mobile devices. On top of that, mobile devices are also more susceptible to both physical and virtual threats from third-party apps and open Wi-Fi.
Importance of Mobile Security
Mobile security involves the use of a combination of strategies, infrastructure, and software to safeguard mobile devices against potential threats. This includes protecting data on the local device, the device-connected endpoints as well as networking equipment.
As mobile devices continue to gain popularity over desktops among users, they have also become increasingly attractive targets for attackers. Therefore, it is important that organisations employ mobile security strategies to counter the different kinds of cyber threats targeting mobile devices despite high overhead costs.
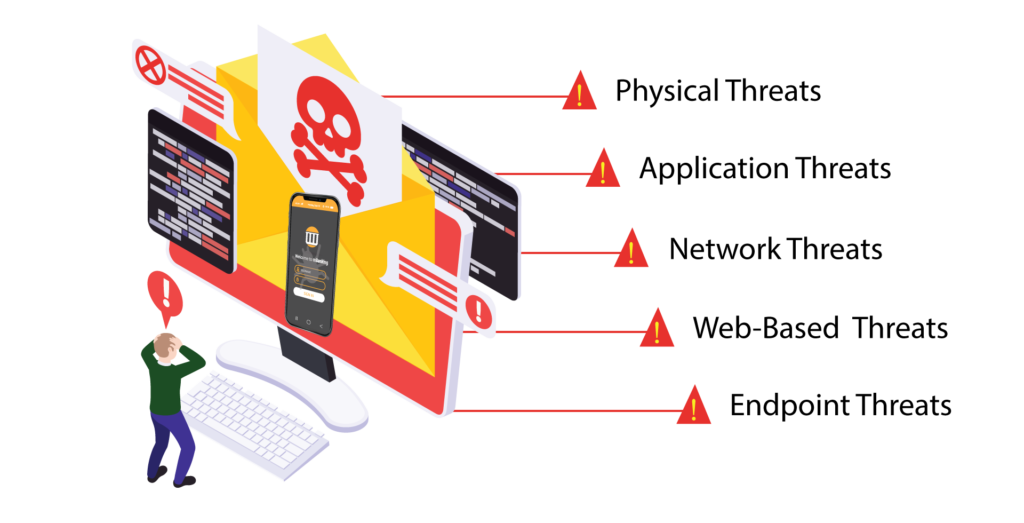
Some examples of cyber threats include Physical Threats, Application Threats, Network Threats as well as Web-based and Endpoint Threats.
Physical Threats
Lost or Stolen Devices are one of the most prevalent mobile threats. The value of a mobile device is not just in its hardware, which can be sold illegally, but also in the potentially sensitive personal and organizational data it could hold.
Application Threats
Downloadable applications can present many types of security issues for mobile devices. Even though these “malicious apps” may seem legitimate when downloaded, they are intentionally created to deceive and defraud users. Some examples of application-based threats include malware, spyware, privacy threats and vulnerable application.
Network Threats
Mobile devices typically support cellular networks as well as local wireless networks (Wi-Fi, Bluetooth). By exploiting weaknesses in the mobile OS or other software used in local or cellular networks, cyber criminals can install malware on your phone without your knowledge.
Web-Based Threats
Attackers use sites that look like official websites tricking users into uploading sensitive data or downloading malicious applications. Users who download the app do not realize that it is a malicious app used to probe the devices for vulnerabilities and disclose data.
Endpoint Threats
Mobile apps connect to data and internal applications using endpoints. These endpoints receive and process data, and then return a response to the mobile device. Endpoints used by the application must be properly coded with authentication and authentication controls to stop and deter attackers. Incorrectly secured endpoints could be the target of an attacker who can use them to compromise the application and steal data to the advantage of the attackers.
Components of Mobile Security
There are several ways in which organisations who use mobile devices can protect themselves from cyber criminals.
Below are some of the components of cybersecurity strategies used to protect organization from attacks directed towards mobile devices:
- Penetration scanners: Automated scanning services can be used to find vulnerabilities in endpoints. While this is not the only cybersecurity that should be used on endpoints, it is the first step in finding authentication and authorization issues that could be used to compromise data security.
- Auditing and device control: While administrators cannot remote control a smartphone or tablet, they can require users to install remote wiping capabilities and tracking services. GPS can be used to locate a stolen device, and remote wiping software will remove all critical data should it be stolen.
- Email security: is one of the biggest threats to any organizations. Email services are usually added to a mobile device so that users can obtain their email messages. Any phishing messages could target mobile devices with malicious links or attachments. Email filters should block messages that contain suspicious links and attachments.
It is also important to create BYOD and mobile device policies that instruct users what can and cannot be installed on the device.
As more users shift from computer to mobile to search for information and services, we see an obvious growing trend in mobile attacks. Businesses are being put at risk for regulatory compliance violations, stolen user data, and more importantly, loss of user trust, bringing irreparable damage to brand reputation.
YESsafe AppProtect+ stays abreast with the ever-evolving malware attacks, is continuously being updated to keep abreast with evolving new threats.
Core Functions

App Shielding
- Protect your app against static and dynamic attacks, preventing tampering, reverse engineering and malware attacks
- Detects and prevents real-time attacks. App shielding protects your app in any environment, including an untrusted environment

Code Protection
- Code obfuscation conceals the logic and purpose of an app’s code, making it harder for an attacker to find vulnerabilities and retrieve sensitive app data
- Code hardening renders your code illegible without affecting its functionality, making the app more resistant to reverse engineering and app tampering, protecting against intellectual property theft, loss of revenue and possible reputational damage
App Data Protection
- Secure Dynamic Data (SDD) – a security feature that enables the storage of sensitive app data (e.g. session tokens, API keys) locally on the end-user devices in a secure and encrypted manner, even on rooted/ jailbreak devices.
- Secure Static Data (SSD) – Protects fixed assets inside your app, such as certificates and API keys. With SSD, assets are automatically encrypted during shielding and only decrypted at application runtime when needed by the application code.

App Scanning
- Scans the app and provide the user with a report highlighting any weaknesses and vulnerability found for the user to review and improve on
- Checks the app’s vulnerability against of the latest list of software and hardware weaknesses database compiled by leading open-source security communities such as OWASP and CWE
App Pulse+
Application threat alarm and analysis:
- Real-time collection of security threats detected by the application and its operating environment
- Provides alarm information, including threat event type, device model, system version, time of occurrence, etc.
- Historical information can be combined on a statistical dashboard for overall analysis.
Application data collection and analysis:
- Collects data on user distribution, user participation, function usage, and performance indicators.
- Helps application owners and enterprises understand the application usage status through customizable statistical reports and dashboards.
- Enables monitoring of user dynamics to control the direction of business development and improve overall performance.
YESsafe AppProtect+ responds promptly to any risk detected on the client side. Fulfilling app protection, risk detection and respond actions requirements, providing the complete app protection cycle.
Find out more about YESsafe App Protect+ when you speak to a specialist today.
